Amazon EKS Core Services
Overview
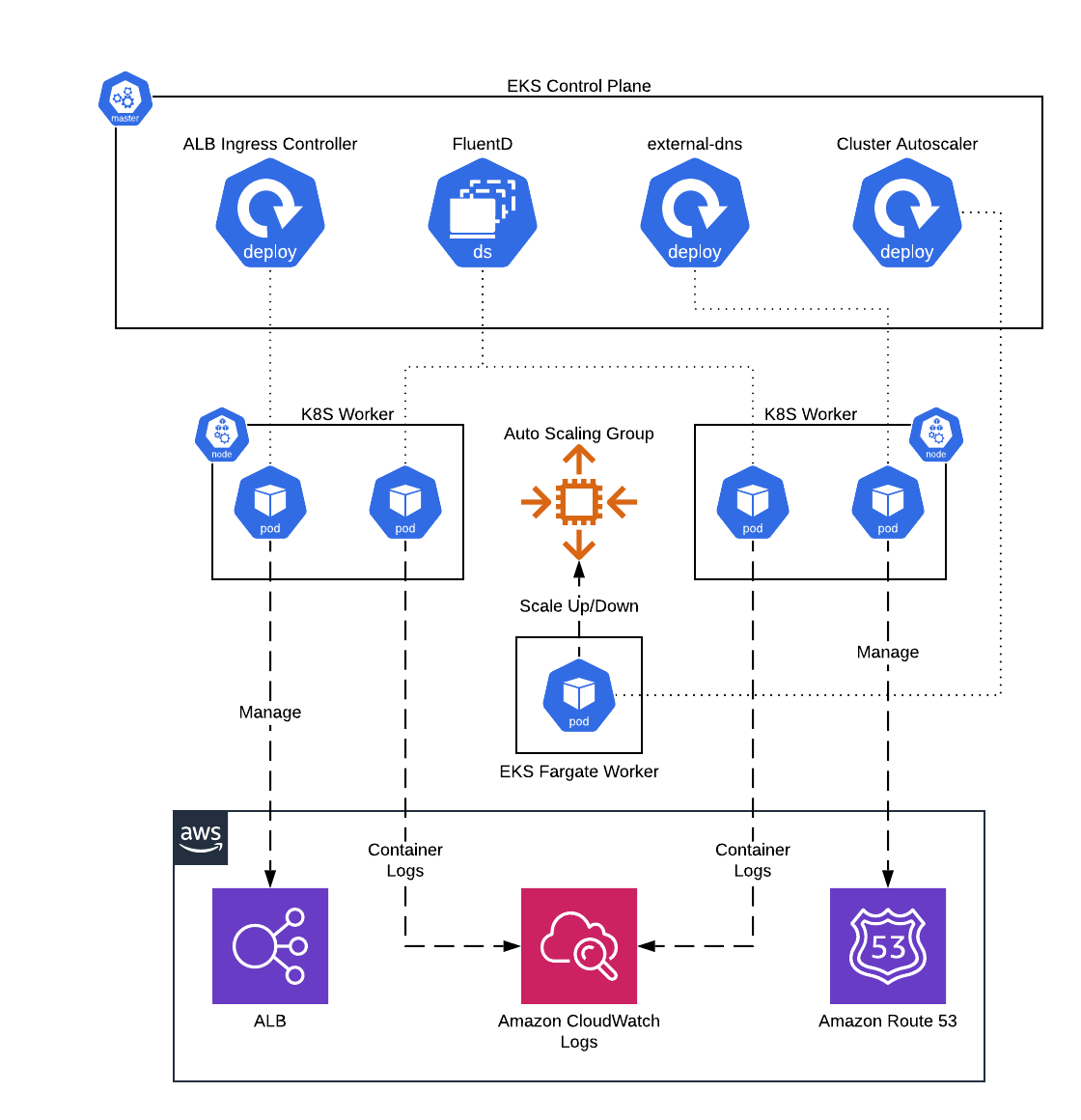
This service contains Terraform and Helm code to deploy core administrative services, such as FluentD and the ALB Ingress Controller, onto Elastic Kubernetes Service(EKS).
 EKS Core Services architecture
EKS Core Services architecture
Features
- Deploy FluentD DaemonSet to ship container logs to CloudWatch Logs
- Deploy ALB Ingress Controller to configure ALBs from within Kubernetes
- Deploy external-dns to manage Route 53 DNS records from within Kubernetes
- Deploy Kubernetes cluster-autoscaler to configure auto scaling of ASGs based on Pod demand
- Deploy AWS CloudWatch Agent to configure container and node level metrics from worker nodes
Learn
note
This repo is a part of the Gruntwork Service Catalog, a collection of reusable, battle-tested, production ready infrastructure code. If you’ve never used the Service Catalog before, make sure to read How to use the Gruntwork Service Catalog!
Under the hood, this is all implemented using Terraform modules from the Gruntwork terraform-aws-eks repo. If you are a subscriber and don’t have access to this repo, email support@gruntwork.io.
Core concepts
For information on each of the core services deployed by this service, see the documentation in the terraform-aws-eks repo.
Repo organization
- modules: the main implementation code for this repo, broken down into multiple standalone, orthogonal submodules.
- examples: This folder contains working examples of how to use the submodules.
- test: Automated tests for the modules and examples.
Deploy
Non-production deployment (quick start for learning)
If you just want to try this repo out for experimenting and learning, check out the following resources:
- examples/for-learning-and-testing folder: The
examples/for-learning-and-testingfolder contains standalone sample code optimized for learning, experimenting, and testing (but not direct production usage).
Production deployment
If you want to deploy this repo in production, check out the following resources:
examples/for-production folder: The
examples/for-productionfolder contains sample code optimized for direct usage in production. This is code from the Gruntwork Reference Architecture, and it shows you how we build an end-to-end, integrated tech stack on top of the Gruntwork Service Catalog.How to deploy a production-grade Kubernetes cluster on AWS: A step-by-step guide for deploying a production-grade EKS cluster on AWS using the code in this repo.
Reference
- Inputs
- Outputs
alb_ingress_controller_pod_node_affinity— Configure affinity rules for the ALB Ingress Controller Pod to control which nodes to schedule on. Each item in the list should be a map with the keyskey,values, andoperator, corresponding to the 3 properties of matchExpressions. Note that all expressions must be satisfied to schedule on the node.
alb_ingress_controller_pod_tolerations— Configure tolerations rules to allow the ALB Ingress Controller Pod to schedule on nodes that have been tainted. Each item in the list specifies a toleration rule.
autoscaler_down_delay_after_add— Minimum time to wait after a scale up event before any node is considered for scale down.
autoscaler_scale_down_unneeded_time— Minimum time to wait since the node became unused before the node is considered for scale down by the autoscaler.
autoscaler_skip_nodes_with_local_storage— If true cluster autoscaler will never delete nodes with pods with local storage, e.g. EmptyDir or HostPath
aws_cloudwatch_agent_image_repository— The Container repository to use for looking up the cloudwatch-agent Container image when deploying the pods. When null, uses the default repository set in the chart. Only applies to non-fargate workers.
aws_cloudwatch_agent_pod_node_affinity— Configure affinity rules for the AWS CloudWatch Agent Pod to control which nodes to schedule on. Each item in the list should be a map with the keyskey,values, andoperator, corresponding to the 3 properties of matchExpressions. Note that all expressions must be satisfied to schedule on the node.
aws_cloudwatch_agent_pod_resources— Pod resource requests and limits to use. Refer to https://kubernetes.io/docs/concepts/configuration/manage-resources-containers/ for more information.
aws_cloudwatch_agent_pod_tolerations— Configure tolerations rules to allow the AWS CloudWatch Agent Pods to schedule on nodes that have been tainted. Each item in the list specifies a toleration rule.
aws_cloudwatch_agent_version— Which version of amazon/cloudwatch-agent to install. When null, uses the default version set in the chart. Only applies to non-fargate workers.
aws_region— The AWS region in which all resources will be created
cluster_autoscaler_pod_annotations— Annotations to apply to the cluster autoscaler pod(s), as key value pairs.
cluster_autoscaler_pod_labels— Labels to apply to the cluster autoscaler pod(s), as key value pairs.
cluster_autoscaler_pod_node_affinity— Configure affinity rules for the cluster-autoscaler Pod to control which nodes to schedule on. Each item in the list should be a map with the keyskey,values, andoperator, corresponding to the 3 properties of matchExpressions. Note that all expressions must be satisfied to schedule on the node.
cluster_autoscaler_pod_resources— Pod resource requests and limits to use. Refer to https://kubernetes.io/docs/concepts/configuration/manage-resources-containers/ for more information. This is most useful for configuring CPU+Memory availability for Fargate, which defaults to 0.25 vCPU and 256MB RAM.
cluster_autoscaler_pod_tolerations— Configure tolerations rules to allow the cluster-autoscaler Pod to schedule on nodes that have been tainted. Each item in the list specifies a toleration rule.
cluster_autoscaler_release_name— The name to use for the helm release for cluster-autoscaler. This is useful to force a redeployment of the cluster-autoscaler component.
cluster_autoscaler_repository— Which docker repository to use to install the cluster autoscaler. Check the following link for valid repositories to use https://github.com/kubernetes/autoscaler/releases
cluster_autoscaler_scaling_strategy— Specifies an 'expander' for the cluster autoscaler. This helps determine which ASG to scale when additional resource capacity is needed.
cluster_autoscaler_version— Which version of the cluster autoscaler to install. This should match the major/minor version (e.g., v1.20) of your Kubernetes Installation. See https://github.com/kubernetes/autoscaler/tree/master/cluster-autoscaler#releases for a list of versions.
eks_cluster_name— The name of the EKS cluster where the core services will be deployed into.
eks_iam_role_for_service_accounts_config— Configuration for using the IAM role with Service Accounts feature to provide permissions to the applications. This expects a map with two properties: `openid_connect_provider_arnand [``openid_connect_provider_url](#openid_connect_provider_url). The `openid_connect_provider_arnis the ARN of the OpenID Connect Provider for EKS to retrieve IAM credentials, while [``openid_connect_provider_url](#openid_connect_provider_url)is the URL. Set to null if you do not wish to use IAM role with Service Accounts.
enable_alb_ingress_controller— Whether or not to enable the AWS LB Ingress controller.
enable_aws_cloudwatch_agent— Whether to enable the AWS CloudWatch Agent DaemonSet for collecting container and node metrics from worker nodes (self-managed ASG or managed node groups).
enable_cluster_autoscaler— Whether or not to enable cluster-autoscaler for Autoscaling EKS worker nodes.
enable_external_dns— Whether or not to enable external-dns for DNS entry syncing with Route 53 for Services and Ingresses.
enable_fargate_fluent_bit— Whether or not to enable fluent-bit on EKS Fargate workers for log aggregation.
enable_fluent_bit— Whether or not to enable fluent-bit for log aggregation.
external_dns_pod_node_affinity— Configure affinity rules for the external-dns Pod to control which nodes to schedule on. Each item in the list should be a map with the keyskey,values, andoperator, corresponding to the 3 properties of matchExpressions. Note that all expressions must be satisfied to schedule on the node.
external_dns_pod_tolerations— Configure tolerations rules to allow the external-dns Pod to schedule on nodes that have been tainted. Each item in the list specifies a toleration rule.
external_dns_route53_hosted_zone_domain_filters— Only create records in hosted zones that match the provided domain names. Empty list (default) means match all zones. Zones must satisfy all three constraints [(var.external_dns_route53_hosted_zone_tag_filters](#(var.external_dns_route53_hosted_zone_tag_filters),external_dns_route53_hosted_zone_id_filters, andexternal_dns_route53_hosted_zone_domain_filters).
external_dns_route53_hosted_zone_id_filters— Only create records in hosted zones that match the provided IDs. Empty list (default) means match all zones. Zones must satisfy all three constraints [(var.external_dns_route53_hosted_zone_tag_filters](#(var.external_dns_route53_hosted_zone_tag_filters),external_dns_route53_hosted_zone_id_filters, andexternal_dns_route53_hosted_zone_domain_filters).
external_dns_route53_hosted_zone_tag_filters— Only create records in hosted zones that match the provided tags. Each item in the list should specify tag key and tag value as a map. Empty list (default) means match all zones. Zones must satisfy all three constraints [(var.external_dns_route53_hosted_zone_tag_filters](#(var.external_dns_route53_hosted_zone_tag_filters),external_dns_route53_hosted_zone_id_filters, andexternal_dns_route53_hosted_zone_domain_filters).
external_dns_sources— K8s resources type to be observed for new DNS entries by ExternalDNS.
fargate_fluent_bit_execution_iam_role_arns— List of ARNs of Fargate execution IAM Roles that should get permissions to ship logs using fluent-bit. This must be provided ifenable_fargate_fluent_bitis true.
fargate_fluent_bit_extra_filters— Additional filters that fluent-bit should apply to log output. This string should be formatted according to the Fluent-bit docs(https://docs.fluentbit.io/manual/administration/configuring-fluent-bit/configuration-file#config_filter.
fargate_fluent_bit_extra_parsers— Additional parsers that fluent-bit should export logs to. This string should be formatted according to the Fluent-bit docs(https://docs.fluentbit.io/manual/administration/configuring-fluent-bit/configuration-file#config_output.
fargate_fluent_bit_log_stream_prefix— Prefix string to use for the CloudWatch Log Stream that gets created for each Fargate pod.
fargate_worker_disallowed_availability_zones— A list of availability zones in the region that we CANNOT use to deploy the EKS Fargate workers. You can use this to avoid availability zones that may not be able to provision the resources (e.g ran out of capacity). If empty, will allow all availability zones.
fluent_bit_extra_filters— Additional filters that fluent-bit should apply to log output. This string should be formatted according to the Fluent-bit docs(https://docs.fluentbit.io/manual/administration/configuring-fluent-bit/configuration-file#config_filter.
fluent_bit_extra_outputs— Additional output streams that fluent-bit should export logs to. This string should be formatted according to the Fluent-bit docs(https://docs.fluentbit.io/manual/administration/configuring-fluent-bit/configuration-file#config_output.
fluent_bit_image_repository— The Container repository to use for looking up the aws-for-fluent-bit Container image when deploying the pods. When null, uses the default repository set in the chart. Only applies to non-fargate workers.
fluent_bit_log_group_already_exists— If set to true, that means that the CloudWatch Log Group fluent-bit should use for streaming logs already exists and does not need to be created.
fluent_bit_log_group_kms_key_id— The ARN of the KMS key to use to encrypt the logs in the CloudWatch Log Group used for storing container logs streamed with FluentBit. Set to null to disable encryption.
fluent_bit_log_group_name— Name of the CloudWatch Log Group fluent-bit should use to stream logs to. When null (default), uses theeks_cluster_nameas the Log Group name.
fluent_bit_log_group_retention— number of days to retain log events. Possible values are: 1, 3, 5, 7, 14, 30, 60, 90, 120, 150, 180, 365, 400, 545, 731, 1827, 3653, and 0. Select 0 to never expire.
fluent_bit_log_group_subscription_arn— ARN of the lambda function to trigger when events arrive at the fluent bit log group.
fluent_bit_log_group_subscription_filter— Filter pattern for the CloudWatch subscription. Only used iffluent_bit_log_group_subscription_arnis set.
fluent_bit_log_stream_prefix— Prefix string to use for the CloudWatch Log Stream that gets created for each pod. When null (default), the prefix is set to 'fluentbit'.
fluent_bit_pod_node_affinity— Configure affinity rules for the fluent-bit Pods to control which nodes to schedule on. Each item in the list should be a map with the keyskey,values, andoperator, corresponding to the 3 properties of matchExpressions. Note that all expressions must be satisfied to schedule on the node.
fluent_bit_pod_tolerations— Configure tolerations rules to allow the fluent-bit Pods to schedule on nodes that have been tainted. Each item in the list specifies a toleration rule.
fluent_bit_version— Which version of aws-for-fluent-bit to install. When null, uses the default version set in the chart. Only applies to non-fargate workers.
pod_execution_iam_role_arn— ARN of IAM Role to use as the Pod execution role for Fargate. Required if any of the services are being scheduled on Fargate. Set to null if none of the Pods are being scheduled on Fargate.
route53_record_update_policy— Policy for how DNS records are sychronized between sources and providers (options: sync, upsert-only).
schedule_alb_ingress_controller_on_fargate— When true, the ALB ingress controller pods will be scheduled on Fargate.
schedule_cluster_autoscaler_on_fargate— When true, the cluster autoscaler pods will be scheduled on Fargate. It is recommended to run the cluster autoscaler on Fargate to avoid the autoscaler scaling down a node where it is running (and thus shutting itself down during a scale down event). However, since Fargate is only supported on a handful of regions, we don't default to true here.
schedule_external_dns_on_fargate— When true, the external-dns pods will be scheduled on Fargate.
service_dns_mappings— Configure Kubernetes Services to lookup external DNS records. This can be useful to bind friendly internal service names to domains (e.g. the RDS database endpoint).
use_exec_plugin_for_auth— If this variable is set to true, then use an exec-based plugin to authenticate and fetch tokens for EKS. This is useful because EKS clusters use short-lived authentication tokens that can expire in the middle of an 'apply' or 'destroy', and since the native Kubernetes provider in Terraform doesn't have a way to fetch up-to-date tokens, we recommend using an exec-based provider as a workaround. Use theuse_kubergrunt_to_fetch_tokeninput variable to control whether kubergrunt or aws is used to fetch tokens.
use_kubergrunt_to_fetch_token— EKS clusters use short-lived authentication tokens that can expire in the middle of an 'apply' or 'destroy'. To avoid this issue, we use an exec-based plugin to fetch an up-to-date token. If this variable is set to true, we'll use kubergrunt to fetch the token (in which case, kubergrunt must be installed and on PATH); if this variable is set to false, we'll use the aws CLI to fetch the token (in which case, aws must be installed and on PATH). Note this functionality is only enabled ifuse_exec_plugin_for_authis set to true.
vpc_id— The ID of the VPC where the EKS cluster is deployed.
worker_vpc_subnet_ids— The subnet IDs to use for EKS worker nodes. Used when provisioning Pods on to Fargate. Required if any of the services are being scheduled on Fargate. Set to empty list if none of the Pods are being scheduled on Fargate.
container_logs_cloudwatch_log_group_name— Name of the CloudWatch Log Group used to store the container logs.